IBPS RRB PO/Clerk Computer Quiz
Computer Knowledge section can help you to improve your overall score if in case other sections are tougher than the expectation. We are providing you with a question set based on the types and patterns of questions asked in the Computer Knowledge section in previous years.
We already rolled the study plan for IBPS RRB MAINS 2019. Computer Quiz of 27th August 2019 covers the topic, Internet and Security.
We already rolled the study plan for IBPS RRB MAINS 2019. Computer Quiz of 27th August 2019 covers the topic, Internet and Security.
Q1. Which of the following refers to the forging of the return address on an e-mail so that the e-mail message appears to come from someone other than the actual sender?
(a) Spoofing
(b) Redacting
(c) Spamming
(d) Pharming
(e) Ransomware
S1. Ans.(a)
Sol. Spoofing is the forging of the return address on an e-mail so that the e-mail message appears to come from someone other than the actual sender.
Q2. Which of the following refers to blacking out portions of the document, usually to protect confidential information, so that it cannot be recovered later?
(a) Redacting
(b) Encrypting
(c) Spoofing
(d) Defacing
(e) Botnet
S2. Ans.(a)
Sol. Redacting means blacking out portions of the document, usually to protect confidential information, so that it cannot be recovered later. The redacted portion of the document has black bars covering the selected text and the text is no longer there.
Q3. A _________ typically connects personal computers within a very limited geographical area, usually within a single building.
(a) LAN
(b) FAN
(c) TAN
(d) WAN
(e) VPN
S3. Ans.(a)
Sol. A local-area network (LAN) is a computer network that spans a relatively small area. Most often, a LAN is confined to a single room, building or group of buildings
Q4. In which type of malicious act, hacker contacts you by phone or email and attempts to acquire your password?
(a) spoofing
(b) phishing
(c) spamming
(d) bugging
(e) None of these
S4. Ans.(b)
Sol. Phishing is a cybercrime in which a target or targets are contacted by email, telephone or text message by someone posing as a legitimate institution to lure individuals into providing sensitive data such as personally identifiable information, banking and credit card details, and passwords.
Q5. While browsing the internet, which of the following key is used for full screen view?
(a) F3
(b) F5
(c) F11
(d) F9
(e) F1
S5. Ans.(c)
Q6. Which of the following type of software secretly collects information about you and your internet habits?
(a) Detectware
(b) Spam
(c) Spyware
(d) Spooling
(e) None of these
S6. Ans.(c)
Sol. Spyware usually finds its way onto your computer without your knowledge or permission. It runs in the background, collecting information or monitoring your activities.
Q7. Which of the following is a common name for the crime of stealing password?
(a) Spooling
(b) Ransomware
(c) Hacking
(d) Spoofing
(e) None of these
S7. Ans.(d)
Sol. spoofing refers tricking or deceiving computer systems or other computer users. This is typically done by hiding one’s identity or faking the identity of another user on the Internet.
Q8. Which of the following device enabling data transfer between two different networks?
(a) Plotter
(b) Joystick
(c) Gateway
(d) Path
(e) None of these
S8. Ans.(c)
Sol. A gateway is a network node that connects two networks using different protocols together.
Q9. Which of the following is related to simplex communication?
(a) Single wire and two-sided communication
(b) Television
(c) Two-wire communication
(d) Walkie-talkie
(e) None of these
S9. Ans.(b)
Sol. Television is an example of simplex communication.
Q10.Which of the following is not a web browser?
(a) Firefox
(b) Safari
(c) FTP
(d) Edge
(e) Both (c) and (d)
S10. Ans.(c)
Sol. File Transfer Protocol (FTP) is not a web browser. It is a standard network protocol used for the transfer of computer files between a client and server on a computer network.










 RBI Grade B Recruitment 2026 Notificatio...
RBI Grade B Recruitment 2026 Notificatio...
 RBI Assistant Score Card 2026, Download ...
RBI Assistant Score Card 2026, Download ...
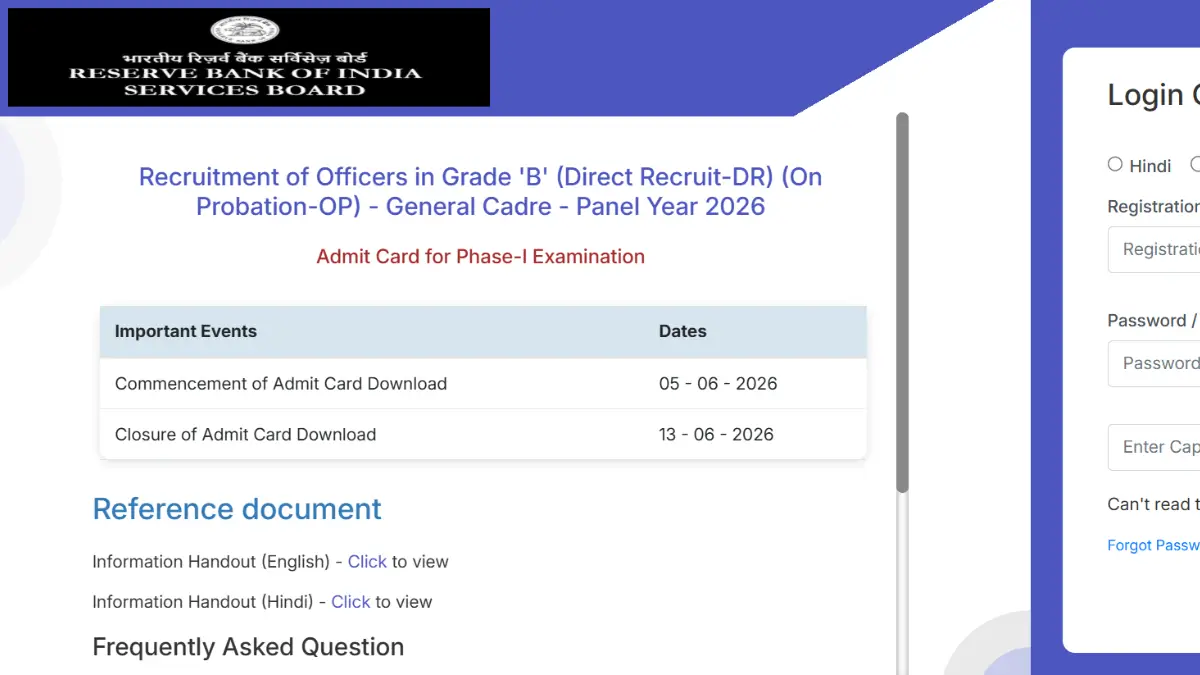 RBI Grade B Admit Card 2026 Out @rbi.org...
RBI Grade B Admit Card 2026 Out @rbi.org...